
Defending the factory floor
March 11, 2024
By Jack Kazmierski
The need for a battle plan to secure operational technology systems in manufacturing
 PHOTO: © Dennis / Adobe Stock
PHOTO: © Dennis / Adobe Stock As today’s manufacturing facilities transition into an evermore complex digital environment, with many adopting Internet of Things (IoT) technologies in order to boost efficiencies, they’re also opening themselves up to hackers and cybercriminals. The ability to connect to the Internet, as well as the convergence between OT and IT, have exposed the modern manufacturing environment to new cybersecurity threats.
“While smart manufacturing technology has ushered in a new era of industry transformation, it has also introduced new cybersecurity challenges,” says Matt Cameron, global product manager of cybersecurity services at Rockwell Automation. “Common risks to OT systems include unclear ownership of OT security, inadequate protection from IT security solutions and the absence of security features and passwords in even some modern IACS products.”
Attacks on OT systems are on the rise, says Matt Bohne, vice-president and chief product cybersecurity officer at Honeywell, and chair of the ISAGCA (International Society of Automation Global Cybersecurity Alliance).
“I don’t see this slowing down,” he adds. “There’s a shift in what the new normal has become, and this means companies need to understand their vulnerabilities and they need to fund and support their cyber programs. The days when they thought about cybersecurity as something ‘they’ll get to’ or something ‘they’ll invest in the next quarter or next year’ are behind us.”
In order to address OT risks, Bohne says that companies need to include remedies in their annual financial plan. “The first order of business is to step back and look at your software and manufacturing operations,” he explains. “Look at the risks that you have there, and make sure you’ve effectively planned upgrades, and that you’ve prioritized those upgrades over other projects that are perhaps lower risk.”
Bohne adds that asking the right questions is critical. “Look at the real risks you’re hosting in your infrastructure,” he explains. “How old is it? Has it been maintained? Have you been doing patching? Have you been making operational changes in the infrastructure? If not, what do you need to do?”
You may need help from some of your vendors, Bohne explains, but it’s vital to come up with a plan of action. “Once you have a plan,” he adds, “you’ll need to fund that plan so that the work actually gets performed. Getting the work done isn’t that hard, but you need to set aside the necessary funding so that the work is completed.”
Mitigating risk
Rockwell Automation’s Matt Cameron says that it’s important for organizations to be vigilant in monitoring and responding to security incidents and that they must take action quickly once a weakness or vulnerability is identified. It’s also important for them to understand the convergence between securing OT and IT environments.
“Creating an effective OT cybersecurity plan for a manufacturing company requires a deep understanding of the organization’s specific risks and vulnerabilities, as well as a comprehensive approach to security that includes people, processes, and technology,” Cameron adds. “It is important to work with experienced OT cybersecurity professionals to ensure that your plan is effective and sustainable over the long term.”
As the factory floor becomes more connected, Cameron explains, there are a number of steps manufacturers can take to secure their OT environments. Cameron recommends the following:
- Implement micro-segmentation: Micro-segmentation can help to further isolate OT systems and reduce the risk of attacks spreading.
- Use Zero Trust security: Zero Trust security is a security model that assumes that no user or device is trusted by default. Zero Trust security can help to protect OT environments from attacks that exploit vulnerabilities in trusted users or devices.
- Use artificial intelligence (AI) and machine learning (ML) for security: AI and ML can be used to detect and respond to OT security threats more effectively.
- Monitor OT networks for suspicious activity: Manufacturers should monitor OT networks for suspicious activity and respond promptly to incidents.
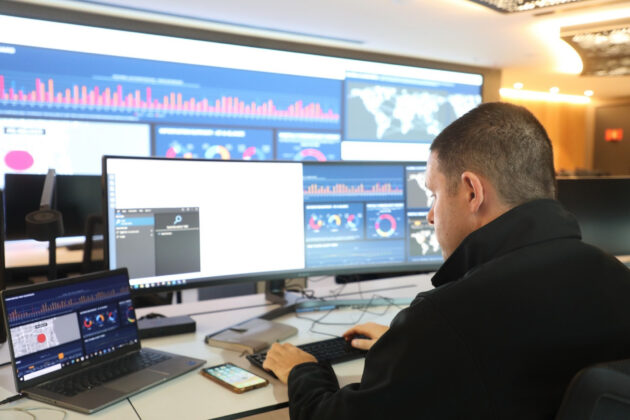
A cyberattack on OT networks can potentially bring the entire manufacturing facility to a standstill. (Photo: Rockwell Automation)
Artificial intelligence and security
The next phase of the war on cybercriminals will likely play out with the help of AI (artificial intelligence). “AI can be used for both good and evil,” says Robert Barton, chief technology officer at Cisco Canada. “On the evil side, people will use AI to impersonate someone in the company so that they can gain access to critical systems. AI can also develop content that is so authentic-sounding and so believable that people will click on a link.”
Cameron agrees. “Adversaries use AI to develop new attacks and malware, draft phishing emails and exploit vulnerabilities,” he says. “On the other hand, organizations can also use AI to protect their OT environments from attack. For example, organizations can use it to detect and respond to OT security threats more effectively. AI can also help organizations automate security tasks, such as threat detection, which can free up security personnel to focus on more strategic initiatives.”
Legacy systems and the future of cybersecurity
Cisco Canada’s Robert Barton explains that one of the challenges facing the manufacturing sector is the age of some of the equipment still in use. “OT has a lot of old gear,” he says. “You’ll find equipment that’s been on the factory floor for over 20 years because they don’t replace it very often. So how do you make that 20-year-old system secure?
“SCADA is the protocol that runs in OT, but it’s a 60-year-old protocol. It runs the world, and it’s basically insecure. We’re trying to build all these wrappers for security around it, and that’s our challenge.”
Thinking about the years ahead, Barton believes that cybersecurity risks are going to continue to mount. “I think it’s getting worse,” he says. “Cybercriminals have new tools, like AI at their disposal, and that makes our job that much more difficult. Five years ago, we weren’t fighting AI. Now we are. And I think for every advance we make in security, the hackers are also making advancements.”
Now, more than ever, it’s vital for manufacturers to have an effective strategy in place as they strive to protect their OT systems from cybercriminals. “With digital transformation and the increased use of interconnected devices, the OT cybersecurity landscape is becoming more complex,” concludes Cameron.
“This complexity brings with it new challenges, such as the need to secure a wide range of devices and systems that are interconnected and that communicate with one another,” he adds. “As a result, it is essential for organizations to have a comprehensive cybersecurity strategy in place that addresses the unique challenges of OT environments and is flexible enough to adapt to changing threats and technologies.”
Improve your cybersecurity posture
Matt Cameron, global product manager of Cybersecurity Services at Rockwell Automation recommends the following steps when securing your OT environment:
- Conduct a risk assessment: Start by identifying and assessing the potential risks and vulnerabilities in your OT environment. This should include identifying critical assets, evaluating the impact of potential threats and understanding the current security posture of your systems.
- Develop a security strategy: Based on the results of the risk assessment, develop a cybersecurity strategy that includes goals, objectives and an action plan. This should include a clear definition of roles and responsibilities, policies and procedures and a framework for measuring success.
- Implement security controls: Once your strategy is in place, it is time to implement security controls to protect your OT environment. This may include access controls, network segmentation, security monitoring, incident response plans and training and awareness programs for employees.
- Continuously monitor and improve: A critical component of any OT cybersecurity plan is ongoing monitoring and continuous improvement. This means regularly reviewing and updating your security controls, testing and validating your security posture, as well as staying up to date on emerging threats and vulnerabilities.
- Work with trusted partners: Companies can collaborate with trusted partners, such as cybersecurity experts and managed security service providers, to help them implement effective security measures and manage cybersecurity risks in their OT environments.
Advertisement
- Cordé Électrique, led by a woman entrepreneur, receives federal support on International Women’s Day
- National Optics Institute receives over $1.2M in federal support to strengthen Quebec’s quantum ecosystem