
SwRI develops technology to detect cyber threats to industrial networks
May 19, 2022
By Manufacturing AUTOMATION
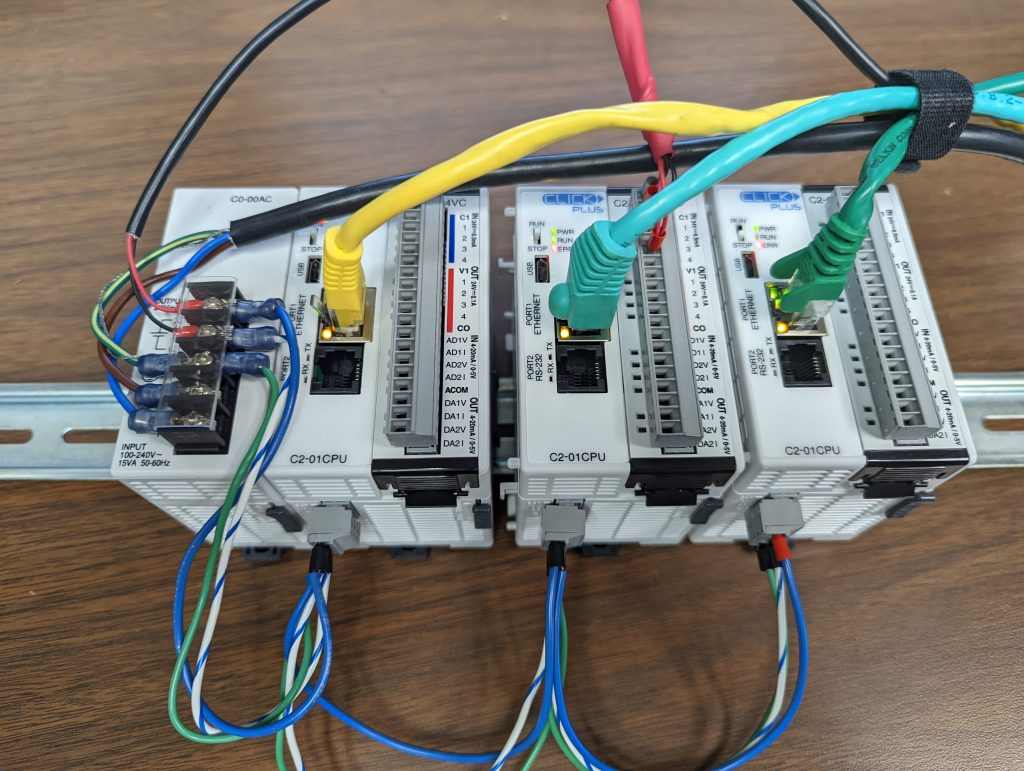 SwRI used programmable logic controllers (PLCs) connected to input/output (I/O) modules to a test network. Algorithms scanned the network for cyberattacks through data packets transferred over the Modbus/TCP protocol. (Photo: SwRI)
SwRI used programmable logic controllers (PLCs) connected to input/output (I/O) modules to a test network. Algorithms scanned the network for cyberattacks through data packets transferred over the Modbus/TCP protocol. (Photo: SwRI) U.S.-based Southwest Research Institute (SwRI) has developed technology that can help detect cyber threats to industrial networks used in manufacturing systems and critical infrastructure. Increasing cyber threats to industrial automation led SwRI to fund this research.
The research team featured experts from SwRI’s Critical Systems Department, which specializes in embedded systems and cyber security, and the Institute’s Manufacturing Technologies Department, which specializes in software and hardware integration for robotics and industrial automation.
SwRI’s team used algorithms to scan for cyber threats across network protocols that transmit industrial control data for everything from manufacturing robots to natural gas pipelines. The team developed an intrusion detection system (IDS) for industrial control systems (ICS) during the course of its research efforts.
“Historically, industrial control systems were not designed with security in mind,” said Ian R. Meinzen, an SwRI intelligent machines engineer who worked on the project. “They had the benefit of an ‘air gap’ where they could operate securely without a connection to IT networks.”
Modern automation systems leverage the internet of things (IoT) to transmit vast amounts of data. It is therefore no longer possible to unplug industrial networks from information technology (IT) networks.
During the course of its research, SwRI focussed on scanning for cyberattacks over the Modbus/TCP protocol. This Ethernet-based networking protocol has been used for decades in supervisory controls and data acquisition (SCADA) systems equipment.
Originally, SwRI researchers originally the algorithms to scan Controller Area Network (CAN) bus networks used in automotive hardware. They customized cybersecurity algorithms to scan a simulated network equipped with industrial devices before evaluating the new algorithms on a real-world industrial network. The test system used the Modbus/TCP protocol to send data packets over a network. The network featured an Ethernet switch that connected personal computers, programmable logic controllers (PLCs) and input/out (I/O) modules. Such industrial computing devices send commands and record data for automated robots and mechanized equipment.
“We had to customize the previous algorithms to recognize the different ways the Modbus/TCP protocol grouped data packets in sequences and time signatures,” said Jonathan Esquivel, an SwRI computer scientist.
The newly developed algorithms applied to the test network recognized normal Modbus/TCP traffic and identified cyberattack vectors such as out-of-band timing, address probing and data fuzzing/manipulation. The algorithms classify data packets as “regular” if they come from an uncompromised industrial control device or “attack” if the source is an unexpected or compromised device.
Advertisement
- Advanced Motion & Controls expands offering with Epson robots
- Ford recalls vehicles including nearly 3,000 SUVs in Canada over fire risk